If you sell into Europe—or simply manage contracts that touch EU residents—buyers increasingly start their evaluation with a single question: Where does the data live? In 2025, answers that emphasize EU data residency, stringent GDPR controls, and verifiable audit trails don’t just pass procurement— they accelerate it. For many legal, finance, and IT stakeholders, “Germany-hosted” has become a powerful trust signal because it implies predictable compliance, rigorous enforcement culture, and lower cross-border transfer risk.
This article unpacks why a GDPR-first, Germany-hosted Contract Lifecycle Management (CLM) platform helps you win deals faster, what a robust security architecture actually looks like, and how to plan a pragmatic 30-60-90 day migration. You’ll also find a vendor due-diligence checklist you can share with InfoSec and Procurement.
Why “Germany-hosted” is a trust signal
1) Data residency clarity. Hosting contract data in Germany gives you a clean story for DPIAs and vendor risk questionnaires: personal data stays within the EU under German jurisdiction. That reduces the legal and operational friction around international transfers and makes sub-processor disclosures simpler.
2) Enforcement culture and standards. Germany’s supervisory authorities are known for strict interpretations of data protection principles. For buyers, that translates into confidence that a provider operating in Germany has to meet high expectations around transparency, purpose limitation, and security of processing.
3) Procurement psychology. Security reviewers often use data-location as an early filter. “EU-hosted (DE)” shortcuts debate, and can trim weeks off legal back-and-forth— especially when compared with architectures dependent on non-EU data centers or complex transfer mechanisms. The smoother the review, the higher your win rate and the lower your cost of sale.
4) Simpler narratives for customers and auditors. Legal and compliance teams need crisp, defensible statements. “Encrypted at rest/in transit, processed in Germany, audited with complete access logs” is easier to defend than a patchwork of regions and exceptions.
Bottom line: Germany-hosted is not a magic badge of compliance—plenty of non-DE hosting can be compliant, too. But it does lower perceived risk and makes the due-diligence story shorter, clearer, and more persuasive.
The security architecture that actually earns trust
Hosting location is only one layer. Buyers care how the platform enforces confidentiality, integrity, and availability—day in, day out.
Encryption in transit and at rest. TLS 1.2+ everywhere; strong ciphers; HSTS; perfect forward secrecy. At rest, modern AES-256 with key management controls, envelope encryption, key rotation, and separation of duties around key access.
Granular, role-based access control (RBAC). Contract work cuts across Legal, Sales, Procurement, and Finance. A trustworthy CLM lets you scope permissions at workspace, folder, contract, and even clause/field level. Typical patterns:
-
Legal can edit terms; Sales can propose redlines; Finance can read pricing; vendors see only the final, shared clauses.
-
Temporary links with expiry; view-only watermarked PDFs for external counsel.
Multi-factor authentication (2FA/MFA) and SSO. Enterprise SSO (SAML/OIDC) plus MFA policies per group/device— and the ability to enforce IP allowlists, device posture checks, and session timeouts.
Audit-ready logs. Every action is attributable: who viewed which contract, who changed which clause, which API client exported what, and when. Logs are tamper-evident, searchable, exportable (e.g., to your SIEM), and retained under a policy you control.
Data minimization and PII hygiene. CLM should support field-level masking, automatic detection of PII (e.g., names, emails, ID numbers) inside attachments, and redaction workflows before external sharing.
High availability and resilience. Redundant storage, point-in-time recovery, tested disaster-recovery RTO/RPO, and documented backup encryption. Trust requires uptime, not just encryption.
Sub-processor transparency. A living list of sub-processors with location and role; contractual safeguards (e.g., DPAs with each); and a change-management process that notifies customers ahead of time.
When you can demonstrate these controls—and prove they’re enforced in Germany—you shift conversations from skepticism to solution value.
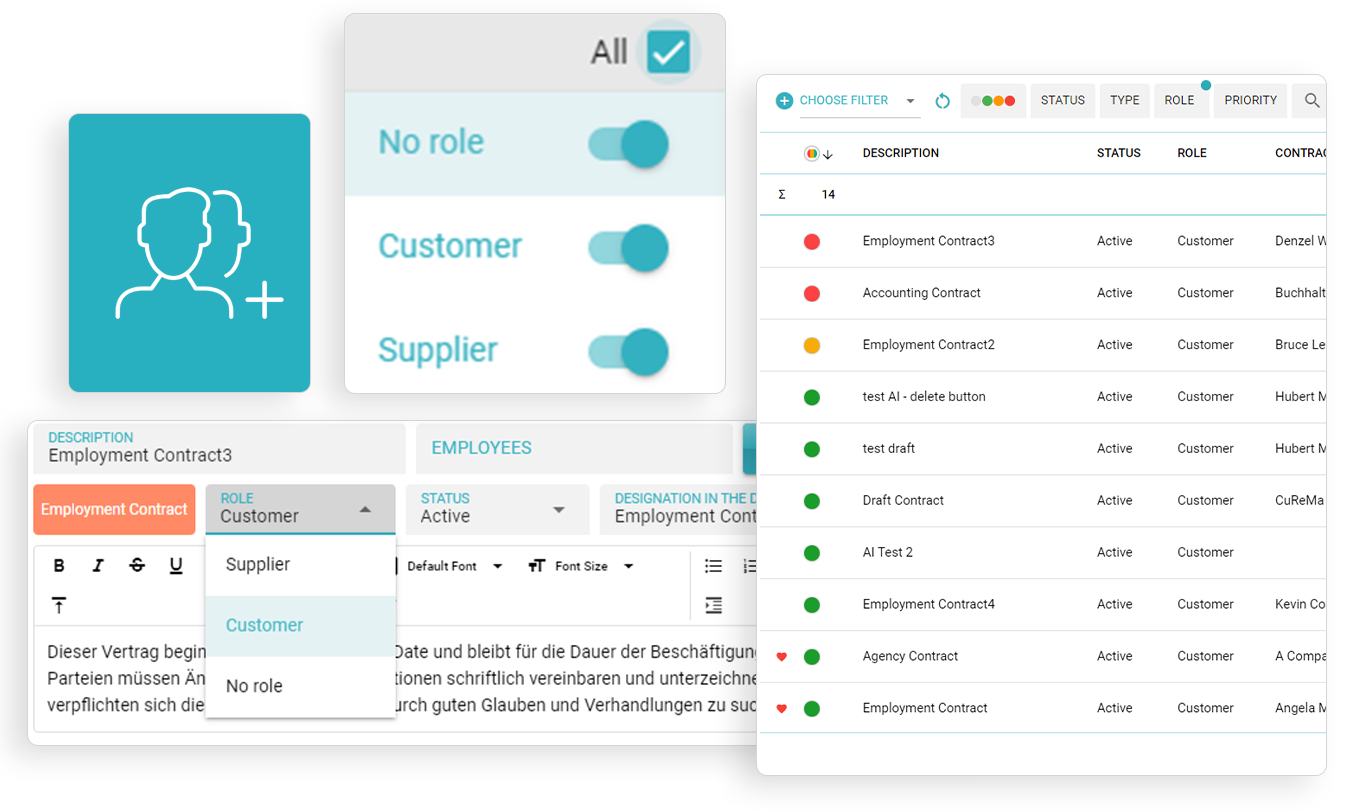
Role-Based Grouping
Easily reach related contracts based on the role.
Group and also list your "no-role" contracts.
Procurement’s vendor due-diligence checklist
Share the following with your buyer’s InfoSec and Legal teams to accelerate review.
Data residency & the DPA
-
Exact hosting region(s), failover regions, and whether any data (including logs/metrics) leaves the EU.
-
A Data Processing Addendum (DPA) defining purpose, categories of data, retention periods, deletion processes, and sub-processor list.
-
Contact points for data subject requests and incident response.
-
Mechanisms for international transfers (ideally not needed if fully EU-hosted; otherwise, SCCs and supplementary measures).
Access logs and retention policy
-
Log schema (actor, action, object, timestamp, IP, client).
-
Retention period options and export formats (CSV/JSON/SIEM).
-
Evidence of immutability or tamper detection.
Integrations (SSO, e-signature, ERP/CRM)
-
SAML/OIDC support; SCIM for user provisioning/deprovisioning.
-
E-signature providers with EU data centers and qualified signatures where needed.
-
Connectors for CRM/ERP (e.g., Salesforce, Dynamics, SAP) with field-level mapping and permission inheritance.
Security management and certifications
-
Vulnerability management cadence, third-party penetration tests, responsible disclosure policy.
-
Statements on ISO 27001/27018, SOC 2 Type II (if applicable), or equivalent controls mapped to GDPR Article 32.
If a vendor can answer these points clearly, reviewers typically move faster—and you close earlier.
Contract Audit
See and follow the changes.Reach the related contract with a click.
Search and download (CSV format). Pro Version
Case study (illustrative): How a Germany-based SME turned compliance into competitive advantage
A mid-market manufacturer selling components across the DACH region struggled with slow legal reviews and skeptical enterprise buyers. Security questionnaires routinely stalled deals for 4–6 weeks. By moving to a Germany-hosted, GDPR-first CLM, they reframed the conversation.
-
Security review time dropped from ~28 days to ~9 days after they standardized on a single due-diligence packet (DPA, sub-processors, RBAC map, audit-log sample exports).
-
Redlines on data-protection clauses decreased by 35% because buyers accepted the standard DPA language once they saw the residency and logging model.
-
Win rate on enterprise opportunities improved by 8–10% quarter-over-quarter as stalled deals cleared.
-
Internal efficiency rose: SSO + RBAC reduced “wrong eyes” incidents to near zero; Finance gained read-only access to price terms, and Procurement could share view-only clauses with suppliers.
These numbers are illustrative, but the pattern is common: when you remove uncertainty around data handling, buyers spend their time on business value instead of risk mitigation.
A pragmatic 30-60-90 day migration plan
Days 0–30: Prove and prepare
-
Inventory & classify. Identify contract repositories (DMS shares, email attachments, e-signature vaults). Tag by counterparty, value, renewal date, and PII presence.
-
DPIA & DPA alignment. Draft/approve your DPIA template and vendor DPA; document hosting region (DE) and sub-processors.
-
Identity foundation. Set up SSO, MFA, and baseline RBAC roles (Legal, Sales, Procurement, Finance, External).
-
Pilot import. Load 200–500 representative contracts. Test search, clause extraction, and logs.
-
Security artifacts. Assemble the evidence pack: architecture diagrams, logging samples, backup/DR summary.
Days 31–60: Operationalize
-
Bulk import & normalization. Migrate the rest; standardize naming, metadata, and folder taxonomy.
-
Clause library & playbooks. Build canonical clause variants (e.g., liability, data protection, price escalators) and redline guidance.
-
Workflows. Configure templates for NDAs, MSAs, and SOWs; enable approval paths and reminders for notice periods and renewals.
-
Training. Role-specific sessions; “how to find anything in 60 seconds” training for Sales and Finance.
Days 61–90: Optimize and integrate
-
Integrations. Wire up CRM/ERP and e-signature; enable SCIM provisioning from your IdP.
-
Monitoring & KPIs. Track cycle time, on-time renewals, review aging, and export audit-log dashboards to your SIEM.
-
Governance. Finalize retention policies, deletion workflows, and quarterly access reviews.
-
Customer-facing narratives. Update your website and proposals with concrete statements: “Hosted in Germany,” “All access logged,” “EU data residency,” plus a link to your DPA.
By day 90, you should have a stable, auditable, and sellable CLM foundation that shifts buyer conversations from “is this safe?” to “how quickly can we go live?”
Measuring ROI: trust as a revenue driver
Traditional CLM ROI focuses on internal efficiency—fewer emails, faster redlines. Those matter. But for teams selling into regulated or risk-sensitive industries, trust is the multiplier:
-
Shorter sales cycles. Each week removed from security review is a week sooner to revenue recognition.
-
Higher close rates. Buyers drop out less often when risk questions are answered early and decisively.
-
Lower legal cost. Fewer bespoke data-protection edits; fewer one-off clauses to maintain.
-
Better renewal performance. With clear logs and notice-period alerts, you prevent accidental renewals and avoid penalties.
-
Audit readiness. When an incident or regulator question arises, you can evidence who accessed what, when, and why—without scrambling.
When trust is embedded into your CLM stack—and you can point to Germany-hosted data, strong RBAC, MFA, and complete logs—it becomes a real commercial advantage.
Choosing a GDPR-first, Germany-hosted CLM is not just a compliance checkbox. It’s a go-to-market strategy. By simplifying due diligence, clarifying data residency, and demonstrating concrete security controls, you remove the friction that slows deals and rattles stakeholders. Pair that with a disciplined 90-day rollout and measurable KPIs, and you’ll find that the same features that make auditors happy also make customers buy.
Next steps:
-
Book a 20-minute GDPR walkthrough of contractSILO.
-
Or start your 14-day EU-hosted trial and see how quickly your team can search, review, and sign with full auditability.
1) What’s the difference between EU-hosted and EU-owned vendors?
EU-hosted refers to the physical and logical location of data processing (e.g., German data centers). EU-owned refers to corporate ownership and control. Both can matter for risk posture and procurement comfort. Many buyers prioritize hosting first because it directly affects data-transfer obligations; ownership is then assessed via governance, sub-processors, and contractual safeguards.
2) Can a non-Germany-hosted solution still be GDPR-compliant?
Yes. GDPR does not mandate German hosting. However, Germany-hosted services often simplify DPIAs and reduce concerns over international transfers and access by non-EU entities. For many organizations, that simplicity translates into faster approvals and fewer legal redlines.
3) How do audit-ready logs actually support compliance and investigations?
Comprehensive logs show who accessed which record, what they did, when, and from where. This helps demonstrate accountability (GDPR Art. 5 & 24), supports incident response, and provides evidence for internal investigations or regulatory inquiries. In practice, searchable, exportable logs cut the time to answer “who saw this?” from days to minutes.
4) What should our DPA include for a CLM platform?
At minimum: processing purpose, categories of personal data and data subjects, retention and deletion processes, security measures (technical/organizational), sub-processor list with locations, incident notification timelines, support for data subject rights, and the lawful basis/transfer mechanism (ideally unnecessary if fully EU-hosted). Clear DPAs reduce negotiation cycles dramatically.
5) How does a GDPR-first CLM protect encryption keys and secrets?
Look for envelope encryption with dedicated key-management (KMS or HSM), strict separation of duties, periodic rotation, and access restricted via least privilege. Keys should never be stored with encrypted data, and access to production secrets should be logged, reviewed, and tied to break-glass procedures.
This article is informational and not legal advice. Work with your counsel and security teams to set requirements appropriate to your industry and jurisdictions.